Immutable Storage
Overview
Recovery plans must include data protection and retrievability. Cyberattacks of any kind can cost companies immense value in lost revenue, reputation and client trust.
(Undefined variable: Series/User_Guide_Online_Help.product_generic) offers two immutable storage features: Secure Snapshots and Retention Lock.
What is Immutable Storage?
Immutable storage is a data security technology that prevents stored information from being modified, overwritten, or deleted for a set period. Often referred to as WORM (Write Once, Read Many), it ensures that once data is written, it remains in its original, pristine state, making it a critical defense against ransomware and accidental data loss.
Benefits of immutable storage include:
-
Ransomware Protection: Prevents malicious actors from encrypting or deleting your backups, ensuring a clean recovery point is always available.
-
Regulatory Compliance: Helps industries like healthcare (HIPAA), finance (SOX, FINRA), and legal sectors meet strict data retention and integrity mandates.
-
Human Error Safeguard: Protects against accidental deletions or misconfigurations by even high-level administrators.
-
Data Integrity: Guarantees that records, such as audit logs or digital evidence, haven't been tampered with since their creation.
What is Ransomware?
Ransomware is a category of cyberattack malware that infects a computer system and restricts access, demanding a ransom to be paid to the malware's creator. Some ransomware encrypts hard drive files. Other types lock the system and display messages requesting payment.

Secure Snapshots
(Undefined variable: Series/User_Guide_Online_Help.product_generic) Secure Snapshots is a simple-to-use, cost-effective feature that allows you to retain and restore complete, secure, incorruptible point-in-time copies of data on your system. This process begins with enabling snapshots for your entire system, then enabling them individually for specific shares, partitions or LSUs, and setting retention periods.
Frequently Asked Questions
Q: What are Secure Snapshots?
A: (Undefined variable: Series/User_Guide_Online_Help.product_generic) Secure Snapshots enable users to create point-in-time physical copies, or snapshots, of the shares, partitions, or LSUs. Each snapshot is timestamped, secured and isolated in a non-network-addressable blockpool located in the (Undefined variable: Series/User_Guide_Online_Help.product_generic) system, enabling fast recovery from ransomware attacks.
Q: What is the difference between Secure Snapshots and Retention Lock?
A: Secure Snapshot allows to system-level immutability at a given point of time. This allows you to retain copies of shares, partitions, and settings on your system. Retention Lock allow file-level immutability within NAS shares. Once a file has a retention lock, it cannot be altered or deleted until the configured lock time period has expired.
Q: How do Secure Snapshots Ensure Security?
A: Snapshots cannot be deleted or changed. There is no datapath access to a snapshot. Attackers cannot use generic attacks on the mounted backup file system, nor can they use the (Undefined variable: Series/User_Guide_Online_Help.product_generic) GUI or RestAPI to access and delete snapshots. There are no referenceable pointers or links to the snapshots or their location to be discovered or otherwise obtained by malware attackers. Data retention is set by the user. Snapshots are only deleted on their set expiration date, which can be individually selected and extended. No interface is provided to access or delete the shares, partitions, or LSUs in the snapshot.
With (Undefined variable: Series/User_Guide_Online_Help.product_generic) Secure Snapshots users are always in control of their data security and retrieveability.
Q: How do (Undefined variable: Series/User_Guide_Online_Help.product_generic) Systems Create Secure Snapshots?
A: After they are enabled for the system then for individual shares, partitions, or LSUs, snapshots are created manually using Command Line Interface (CLI) commands or in the (Undefined variable: Series/User_Guide_Online_Help.product_generic) GUI, using the Scheduler. The (Undefined variable: Series/User_Guide_Online_Help.product_generic) makes a copy of the enabled shares, VTL partitions, or OST LSUs, to be retained for a set period of time.
See Enabling Secure Snapshots for instructions on how to get started enabling the feature and scheduling snapshots in the (Undefined variable: Series/User_Guide_Online_Help.product_generic) User Interface (UI), for specific shares, VTLs or OST LSUs.
Q: How do Users Recover Snapshot Data?
A: A point-in-time snapshot is identified and restored from the GUI, restoring the share, partition, or LSU to its state before the attack. This latest uncorrupted snapshot is unpacked into a new share, partition, or LSU, with either the original name or a new name. Snapshots to be recovered are selected by the customer per their analysis of the attack on their business.
You can restore snapshots in the (Undefined variable: Series/User_Guide_Online_Help.product_generic) User Interface (UI) on specific shares, VTL partitions or OST LSUs.
Tasks
The processes for enabling and scheduling secure snapshots is detailed in the following topics:
Retention Lock
Retention Lock is a data protection feature that enforces immutability at the file level. It ensures that once a backup file is written, it cannot be altered or deleted until its specified retention period expires.
Note: The retention lock feature is currently available for individual files within a NAS share using the NFS protocol with deduplication enabled.
Frequently Asked Questions
Q: What is the difference between Secure Snapshots and Retention Lock?
A: Secure Snapshot allows to system-level immutability at a given point of time. This allows you to retain copies of shares, partitions, and settings on your system. Retention Lock allow file-level immutability within NAS shares. Once a file has a retention lock, it cannot be altered or deleted until the configured lock time period has expired.
Q: Does Retention Lock support regulatory compliance?
A: Retention Lock meets and supports the following regulatory standards: SEC 17a-4(f), CFTC Rule 1.31b, FDA 21 CFR Part 11, Sarbanes-Oxley Act, IRS 98025 and 97-22, ISO Standard 15489-1, and MoREQ2010.
Tasks
The processes for enabling and applying retention lock to NAS files is detailed in the following topics:
To see if retention lock is enabled or disabled on the system, go to Configuration > System > Immutable Storage. The Manage Retention Lock will indicate that it is enabled or disabled. If it is disabled, you must first enable Secure Clock (see Enable Secure Clock).


To enable the file retention lock feature on a NAS, the following requirements must occur:
| Retention Lock | Retention Lock must be enabled (see View Retention Lock Status). |
| NAS Share |
NAS share must use the NFS protocol. NAS share must have deduplication enabled. |
-
To enable retention lock to a new NAS share, see Adding a NAS Share
-
To enable retention lock to an existing NAS share, see Editing a NAS Share
Note: To enable retention lock to an existing NAS share, the share must have deduplication enabled when it was created.
To manually enable retention lock on files within a NAS share, do the following:
-
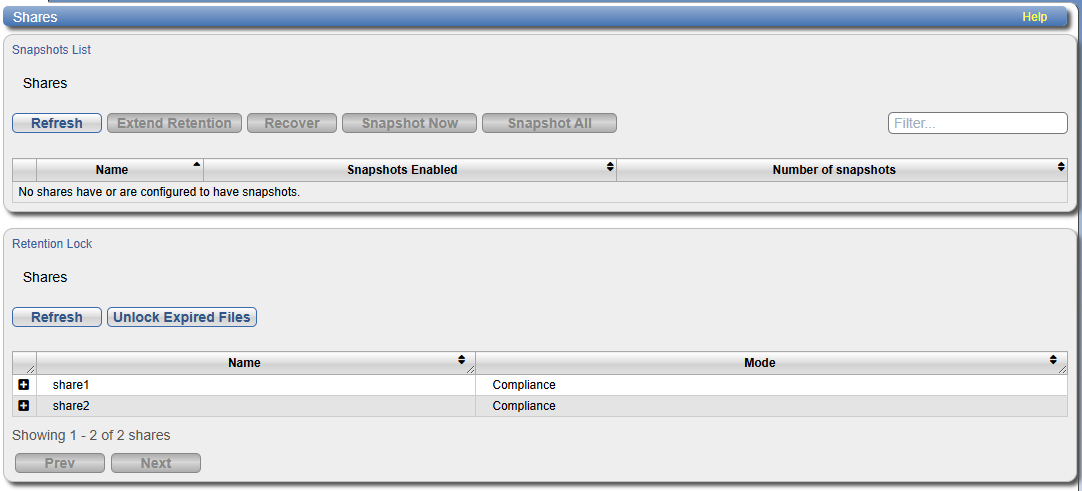
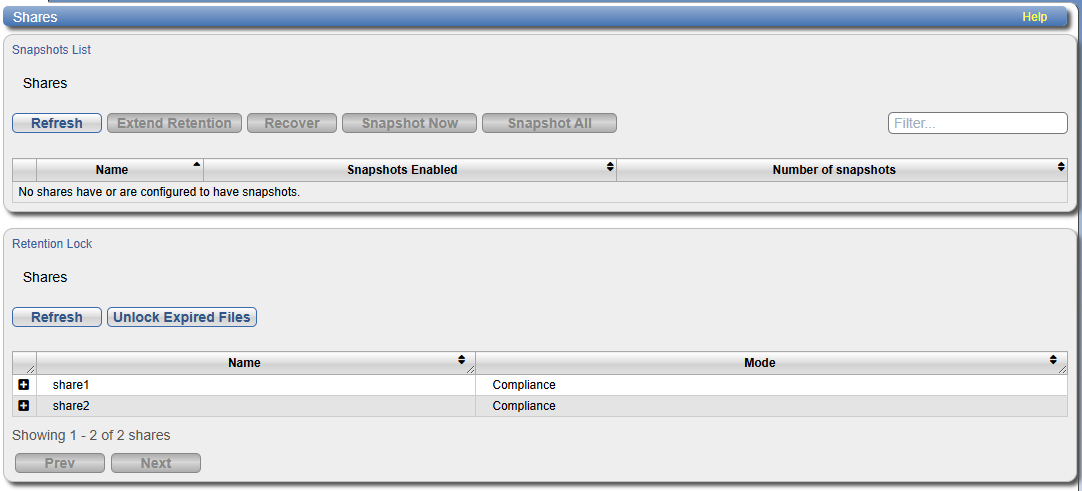
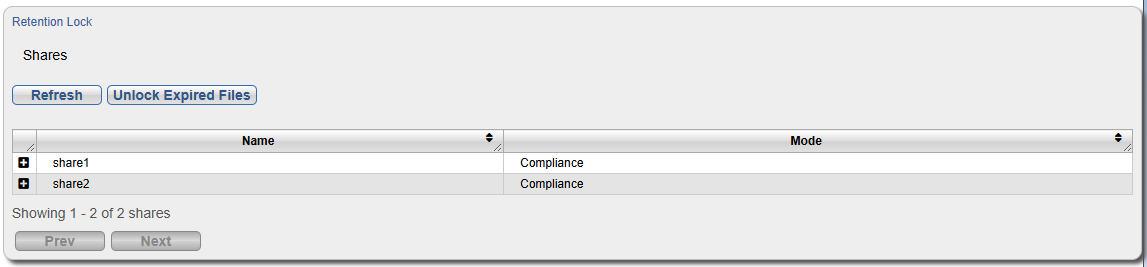
Click the Immutable Storage menu option, and then click the Shares tab.
-
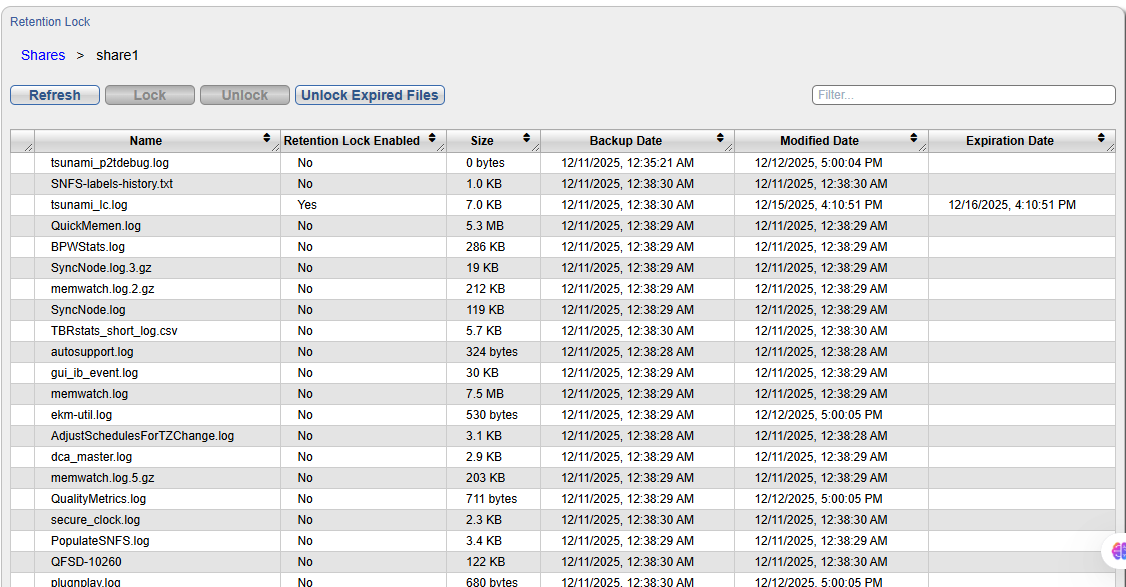
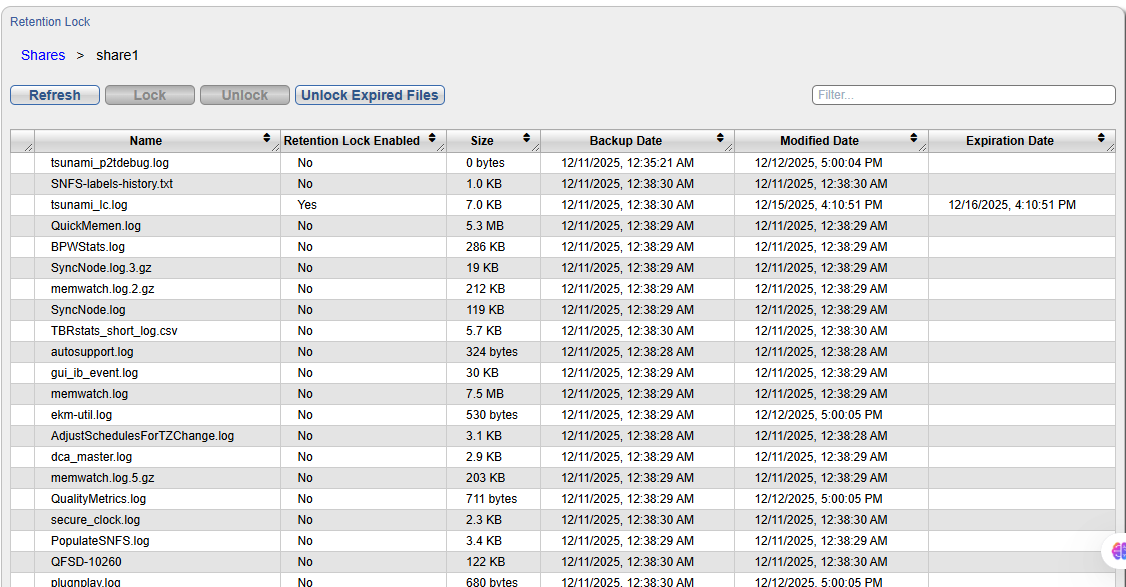
Under Retention Lock, select the NAS share you wish to retention lock files by selecting the + icon next to the share. A list of all files in the share appears.
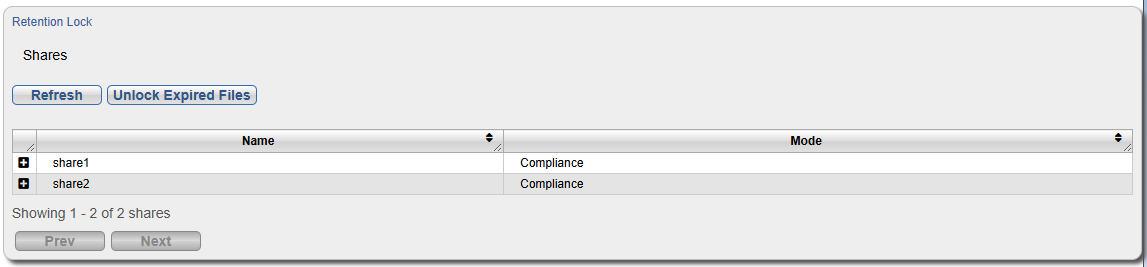
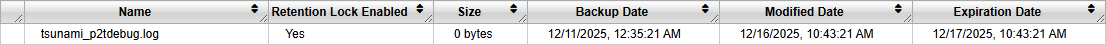
Each retention lock file contains the following information:
Name Name of file in the selected share. Retention Lock Enabled Indicates if retention lock is enabled on the file. Size File size. Backup Date Last time that the file was backed up. If you are using file retention autolock, you will want make the auto lock delay exceed the difference between the backup date and modified date. Modified Date Last time that the file was modified.
If you are using file retention autolock, you will want make the auto lock delay exceed the difference between the backup date and modified date.
Lock Date Date that file was lock. Expiration Date Date that file lock expires. -
Select the file you wish to retention lock and click the Lock button. The Confirm Lock dialog box appears.
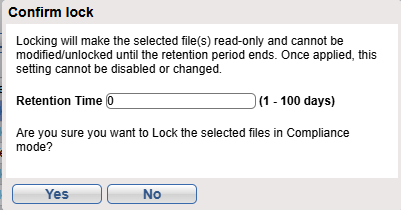
-
Enter the retention time that the file will be locked. The time must be within the specified range documented.
-
Click Yes. The selected file will now have Retention Lock Enabled status of Yes and a retention Expiration Date. The file cannot be altered or deleted until its specified retention period expires.
Note: Files with retention lock enabled cannot be unlocked until the lock expiration date has occurred.
To manually unlock retention lock on files within a NAS share, do the following:
-
Click the Immutable Storage menu option, and then click the Shares tab.
-
Under Retention Lock, select the NAS share you wish to unlock files by selecting the + icon next to the share. A list of all files in the share appears.
-
There are two different options to unlock files: Unlock and Unlock Expired Files:
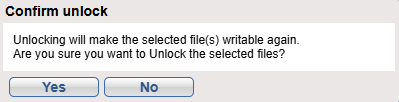
Unlock
Use this to unlock selected files with expired locks.
-
Select the file you wish to unlock and click the Unlock button. The Confirm Unlock dialog box appears.
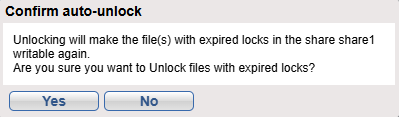
Unlock Expired Files
Use this to unlock all files in the share with expired locks.
-
Click the Unlock Expired Files button. The Confirm Auto-Unlock dialog box appears
-
-
Click Yes. The selected file(s) will now have Retention Lock Enabled status of No and no retention lock Expiration Date.
 minute read
minute read
